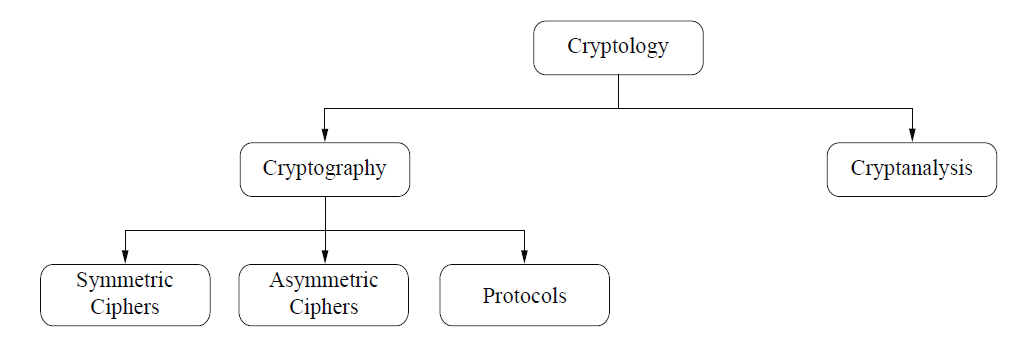
Cryptography is the science of secret writing with the goal of hiding the meaning of a message.
Cryptanalysis is the science and sometimes art of breaking cryptosystems. You might think that code breaking is for the intelligence community or perhaps organized crime, and should not be included in a serious classification of a scientific discipline. However, most cryptanalysis is done by respectable researchers
in academia nowadays. Cryptanalysis is of central importance for modern cryptosystems: without people who try to break our crypto methods, we will never
know whether they are really secure or not. See Sect. 1.3 for more discussion about this issue.
Cryptography itself splits into three main branches:
Symmetric Algorithms are what many people assume cryptography is about:
two parties have an encryption and decryption method for which they share a secret key. All cryptography from ancient times until 1976 was exclusively based
on symmetric methods. Symmetric ciphers are still in widespread use, especially for data encryption and integrity check of messages.
Asymmetric (or Public-Key) Algorithms In 1976 an entirely different type of cipher was introduced by Whitfield Diffie, Martin Hellman and Ralph Merkle. In
public-key cryptography, a user possesses a secret key as in symmetric cryptography but also a public key. Asymmetric algorithms can be used for applications
such as digital signatures and key establishment, and also for classical data encryption.
Cryptographic Protocols Roughly speaking, crypto protocols deal with the application
of cryptographic algorithms. Symmetric and asymmetric algorithms can be viewed as building blocks with which applications such as secure Internet communication can be realized. The Transport Layer Security (TLS) scheme, which is used in every Web browser, is an example of a cryptographic protocol.
Strictly speaking, hash functions form a third class of algorithms but at the same time they share some properties with symmetric ciphers.
In the majority of cryptographic applications in practical systems, symmetric and asymmetric algorithms (and often also hash functions) are all used together. This is sometimes referred to as hybrid schemes. The reason for using both families of algorithms is that each has specific strengths and weaknesses.